VoIP Integration with Other Business Tools: Seamless Collaboration
VoIP Integration with Other Business Tools: Seamless Collaboration Effective communication is vital for any business looking to thrive
VoIP Integration with Other Business Tools: Seamless Collaboration Effective communication is vital for any business looking to thrive
Unveiling the Power of IT Sales Strategies: Tips and Tricks In the fast-paced world of technology, IT companies
The Art of Seamless Integration: Why Your Business Needs Specialists Running a successful business requires various skills and
Integrating Custom Software into Your Existing Systems: Tips and Tricks Integrating custom software into your existing systems can
How Managed IT Support Can Save Your Business Time and Money In today’s digital age, proper management and
Common Access Control Mistakes and How to Avoid Them Introduction Access control is a critical element in ensuring
The Environmental Impact of Automation: Going Green with Smart Processes Moving Towards a Sustainable Future In today’s rapidly
How to Build a Robust Security Culture within Your Organization Welcome to the digital age where organizations face
The Future of Business Customization: Embracing Change with Custom Development In today’s rapidly evolving business landscape, embracing change
VoIP Security: Safeguarding Your Business Conversations In today’s digital era, Voice over Internet Protocol (VoIP) has become an
Today, businesses require IT support services that go beyond the traditional. From cloud-based solutions to AI-driven automation, tech teams are reimagining the future of IT support. We interviewed experts for their insights into the latest trends and how they’ll shape the future of business IT support.
Case Study: Learn how placing custom software at the heart of business operations enabled one organization to transform their operations and reap significant return on investment.
Developing an idea into a reality can be daunting – but it doesn’t have to be. Learn how the custom development process can make the process smoother and take your ideas to fruition.
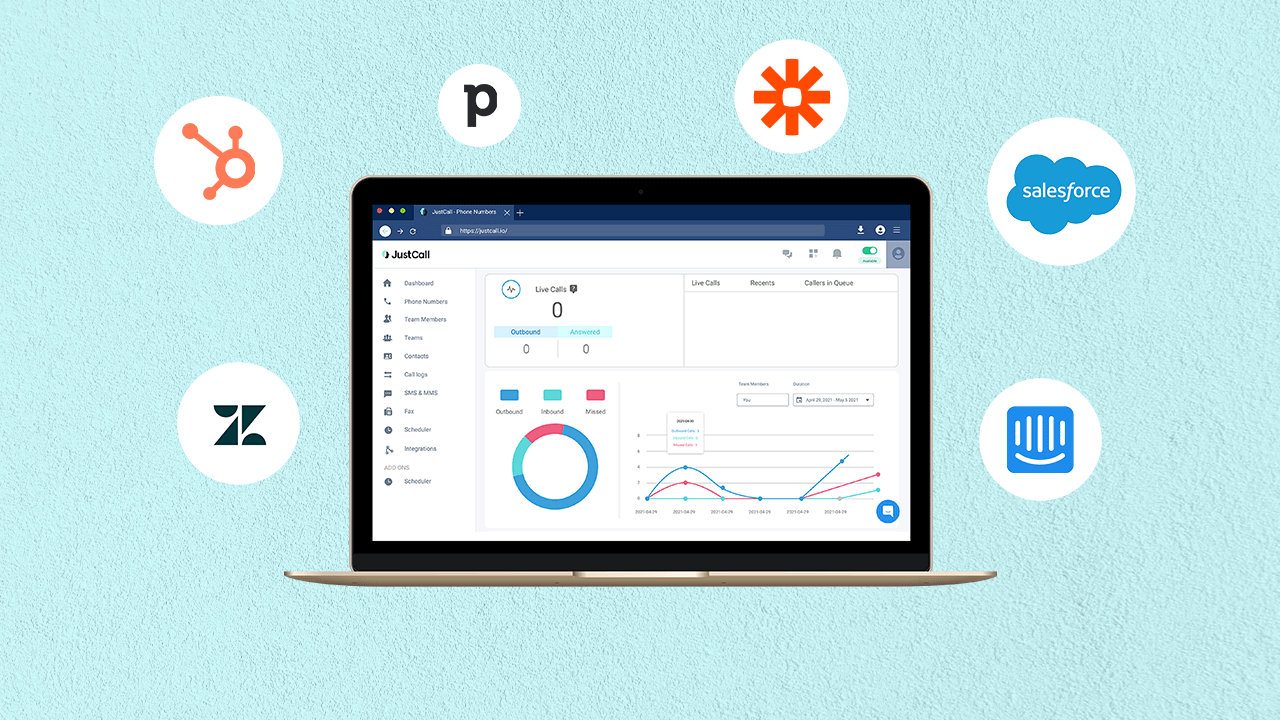
VoIP integration helps to facilitate seamless collaboration amongst disparate tools by connecting different software systems, services, and cloud environments into unified communications environments. This makes it easier to move from one platform to another without interrupting workflow.

Developing a website can seem intimidating, but with the right guidance and tools it doesn’t have to be. Creating a user-friendly website with engaging content and attractive design doesn’t have to be a challenge.

Business process automation has revolutionized the way companies work, eliminating mundane tasks and boosting efficiency and productivity. By embracing this powerful tool, companies are unlocking untapped potential in their daily operations.
Reality is the ultimate goal when it comes to custom development projects, and navigating the process between idea and success can be intimidating. This article demystifies the process, helping you quickly go from idea to reality.

The world is rapidly evolving in terms of technology, with new trends and innovations emerging each day. This ever-evolving landscape is driving waves of progress across all sectors and industries, changing the way we live, work, and communicate.
In today’s age of digital connectivity, having a powerful online presence is essential for businesses of all sizes. Professional website development is the key to establishing a successful online presence. With an effective website, businesses can promote their services, engage customers, and increase their profits.
Ensuring your website’s hosting uptime is vital for businesses. Not only does it keep customers engaged and returning, but it also maintains crucial communication required for everyday business operations. Improving uptime should be a priority for any enterprise.
As technology rapidly evolves and new possibilities emerge, various emerging trends and innovative solutions in the tech sphere are set to revolutionize the future. From the construction of 5G networks to the use of AI solutions, the future of technology is sure to bring exciting and transformative changes.
Data silos are a common cause of inefficiencies and poor collaboration across business units. Fortunately, by leveraging integration solutions, business owners can easily unlock their data silos, allowing organizations to make decisions based on centralized data.
When it comes to digital security, access control is key. Common mistakes such as weak authentication, default settings, and lack of periodic auditing can lead to serious data breaches. Taking the time to properly implement access control strategies can protect sensitive data and ensure system security.
When looking for a hosting provider for your business website, be sure to consider factors such as the cost, customer service, and platform compatibility. Choosing the right provider can make or break your site and ensure your customers have a smooth experience.
Integration of processes, technologies and teams has become an essential component for modern businesses. While understanding the Return On Investment (ROI) of a given integration strategy is essential, it can also be challenging to measure. This article will explore how to systematically track the success and measure the impact of an integration effort.
Workflow automation can optimize team performance and streamline processes, but there are best practices to observe for achieving optimal results. Learn how to improve efficiency and maximize results from workflow automation.
For businesses, web hosting is a critical decision. Choosing the right type of hosting can lead to improved performance, scalability, cost-efficiency, and flexibility. Understanding the differences between shared and dedicated hosting is crucial for making the right choice.
In any organization, access control must be taken seriously. Common mistakes include poor password policies and failing to restrict access to sensitive data. Taking the right precautions can prevent data breaches and unauthorized access.
When evaluating web hosting costs, it’s important to understand additional fees and charges to ensure you get the best value for your money. Understand what you’re paying for and identify hidden fees to ensure that you purchase the right hosting package for your needs.
Custom development allows companies to tailor their online presence to specific needs, creating unique solutions to maximize efficiency and create a competitive edge.
This case study looks at how a website development project transformed a business’s operations and bottom line. Specific strategies used, key successes, and lessons learned are all discussed to provide practical guidance for businesses looking to replicate these results.
Easily managed access control systems are essential for any business; they ensure only authorized personnel can enter secure areas, helping to keep your business secure from external threats.
VoIP technology is revolutionizing how people communicate around the world. Starting as a hobbyist project, VoIP technology has evolved and grown to power global businesses, enabling more efficient communication and collaboration.
Efficiently running a business requires integrating multiple systems. WorkFlow360 CRM allows you to streamline and automate processes, simplifying the task of connecting your existing systems. With seamless integration, you can maximize your productivity and increase your efficiency.
Having reliable IT support is essential for businesses in today’s technology-driven world. Here are the top 10 reasons why professional IT support is essential for your business.
Custom development is an advantageous approach to software and digital product development. It enables organizations to create unique, tailored applications to meet their specific needs, leading to improved efficiency and business success.
Maintaining secure conversations is essential for businesses of all sizes. In this article, we look at the different security protocols available to ensure your VoIP network is safe and your conversations remain confidential.
In the digital kingdom, where gigabytes reign supreme, IT support plays a pivotal role in the mystical realm of data center management. Armed with their knowledge and expertise, these guardians of technology keep the gears turning and wizards of data at ease. Without their watchful eyes and quick-witted minds, chaos would engulf the kingdom, and data would run amok like wild unicorns. From troubleshooting magical machines to conjuring up innovative solutions, IT support is the unsung hero of data center management, ensuring the kingdom’s prosperity in this brave new digital world.
VoIP, the modern voice communication technology, revolutionizes the way businesses connect with clients. Implementing it successfully requires careful consideration and planning. By following these tips, you can ensure a seamless transition to VoIP, empowering your business with cost-effective and efficient communication solutions.
In the ever-evolving business landscape, communication is key. Enter VoIP, a game-changer for businesses worldwide. Say goodbye to traditional phone lines, and hello to cost savings, flexibility, and seamless connectivity. Whether it’s video conferencing or virtual call centers, VoIP offers businesses a myriad of benefits. Embrace the power of VoIP and watch your business soar to new heights.

In today’s digital era, cloud-based collaboration tools have revolutionized the way teams work together, breaking down barriers of distance and time. These tools not only enhance productivity but also foster creativity and innovation. With real-time document sharing, seamless communication, and project management features, businesses can now collaborate effortlessly, achieving more in less time. Embrace the power of the cloud and elevate your team’s productivity to new heights.
Access control is the silent guardian of security, standing tall to protect valuable assets. Like a secret agent, it grants or denies entry with precision and accuracy. Understanding its importance is crucial in the ever-evolving world of security. Let’s delve into this covert operation and unravel its secrets, ensuring a secure future for all.
In today’s digital age, retail businesses are increasingly turning to cloud solutions for streamlined inventory management and seamless point of sale operations. From real-time inventory tracking to efficient customer transactions, cloud-based solutions empower retailers to thrive in a competitive market. Discover how embracing the cloud can revolutionize your retail business, ensuring success for years to come.
In the bustling world of shared office spaces, ensuring access control is crucial for maintaining a harmonious and secure environment. From digital key cards to biometric scanners, innovative solutions are being employed to safeguard against unauthorised entry. As the lines between personal and communal workspaces blur, finding the perfect balance between convenience and security remains a top priority. With technology as our ally, we can create a future where flexibility and privacy coexist seamlessly.
In the digital era, educational institutions face an uncharted territory riddled with IT challenges. The demand for seamless connectivity, data security, and efficient systems pose a unique set of obstacles. However, innovative solutions like cloud-based platforms, robust cybersecurity measures, and personalized tech support can effectively navigate this labyrinth, ensuring a smooth and productive learning environment for students and educators alike. The key lies in embracing the ever-evolving landscape of IT support, revolutionizing educational institutions towards a tech-savvy future.
The world of e-commerce is a fast-paced and ever-evolving landscape. With online businesses relying heavily on technology, the role of IT support becomes crucial. However, supporting e-commerce ventures comes with its own set of unique challenges. From ensuring seamless website functionality to protecting customer data, IT experts must navigate through a myriad of complexities. In this article, we delve into the specific challenges faced by IT support teams in the e-commerce industry, and how they overcome them with innovation and expertise.

In today’s fast-paced digital era, businesses are continually seeking ways to enhance efficiency. Enter workflow automation in the cloud – a game-changer! With this transformative technology, mundane and repetitive tasks can be seamlessly automated, freeing up valuable time and resources. Discover how this innovative solution can streamline your operations and propel your business to new heights. Harness the power of the cloud and unlock your true potential with workflow automation.
In today’s fast-paced digital world, IT support plays a crucial role in keeping businesses running smoothly. Enter proactive monitoring, the unsung hero. With its ability to detect issues before they become critical, it saves time, money, and headaches. From preventing downtime to ensuring optimal performance, proactive monitoring is a game changer for modern IT support. So, embrace the power of foresight and let proactive monitoring redefine your IT success story.
In a world of uncertainties, startups and small businesses require efficient and cost-effective communication solutions. Enter VoIP, the knight in shining armor. From slashing phone bills to enhancing productivity, this technology is a game-changer. Embrace the power of virtual voice communication and watch your business soar to new heights.
The era of physical paperwork, cluttered filing cabinets, and lost documents is long gone. Thanks to cloud-based document management systems, businesses can now effortlessly store, organize, and access their important files anytime, anywhere. This revolutionary technology streamlines workflows, enhances collaboration, and boosts productivity, while bidding farewell to the chaos of traditional paper-based systems. Say hello to the future of efficient document management in the cloud!
In the ever-changing digital landscape, the role of proactive IT support for businesses cannot be overlooked. Just like a vigilant guardian, proactive IT support ensures smooth operations, protects against potential threats, and maximizes productivity. By anticipating issues before they arise, this forward-thinking approach saves time, money, and resources. In today’s competitive world, having proactive IT support is not a luxury but a necessity for any thriving business. Embrace it, and watch your business soar to new heights!
Looking to revolutionize your call center operations? Look no further than VoIP! With its innovative features and endless benefits, VoIP is the game-changer you’ve been waiting for. Say goodbye to traditional phone systems and hello to seamless communication, enhanced customer experience, cost savings, and scalability. It’s time to dial up success with VoIP for call centers!
In an ever-evolving world, ensuring physical security is paramount. Access control systems have emerged as the knight in shining armor. From biometric identification to keyless entry, these marvels of technology provide a seamless solution to safeguard sensitive areas. With their ability to restrict unauthorized access and provide a comprehensive audit trail, enhancing physical security has never been more efficient. Embrace the power of access control and bid farewell to security concerns, one locked door at a time.

In a world propelled by advancing technology, businesses are constantly seeking innovative solutions to drive growth. Enter cloud computing – a game-changer that promises seamless scalability, enhanced efficiency, and unparalleled accessibility. Harnessing the power of cloud solutions enables businesses to streamline operations, maximize productivity, and foster collaboration. Whether small or large, embracing the cloud is the key to unlocking endless possibilities in this ever-evolving digital era.
In the realm of technology, troubleshooting is an art. IT professionals are the knights in shining armor rescuing us from the clutches of technical nightmares. From the infamous blue screen to connectivity hiccups, this article dives into the world of IT support, unveiling the secrets behind resolving common technical issues. So, take a deep breath, for here comes the troubleshooters’ guide to solving tech troubles with finesse.
In today’s digital age, the traditional office setting is evolving rapidly. With the rise of mobile workforces, the need for flexibility and mobility in communication is more important than ever. VoIP, or Voice over Internet Protocol, is a game-changer in this regard. It allows employees to connect and collaborate seamlessly regardless of their physical location. This innovative technology enables businesses to stay efficient and productive in the face of changing work dynamics. Join us as we delve into the world of VoIP for mobile workforces and explore the benefits it brings to the table.
In an increasingly digital world, securing your business data is paramount. With cyber threats on the rise, it’s crucial to implement best practices for IT support. From robust firewalls to regular data backups, safeguarding your information is a creative dance between technology and strategy. This article explores the top practices that will keep your data safe and your business thriving. Stay tuned for expert advice from industry leaders!
In a world where digitalization has become the norm, designing effective workflows is crucial. Cloud integration offers endless possibilities to streamline processes, improve collaboration, and boost productivity. Embracing this technology empowers businesses to create a seamless and efficient work environment. Let’s explore the art of designing effective workflows with cloud integration.
Finding the perfect IT support provider can be a daunting task, like searching for a needle in a digital haystack. But fear not! By following these golden rules of selection, you’ll be able to navigate the IT labyrinth with ease. From assessing expertise to scrutinizing costs, this guide will illuminate your path towards IT support nirvana. Let the quest begin!
As multi-location businesses continue to expand, the importance of robust access control systems becomes paramount. From corporate buildings to retail stores, ensuring authorized personnel have seamless entry while keeping out uninvited guests is crucial. With advanced technologies like biometric authentication and centralized management, these systems offer a perfect blend of convenience and security. By implementing tailored access control solutions, businesses can safeguard their assets, protect sensitive data, and maintain smooth operations across all locations. Stay one step ahead in the multi-location game with state-of-the-art access control systems.
In today’s ever-evolving world of remote work, effective IT support is the backbone of seamless operations. From troubleshooting technical glitches to ensuring secure data sharing, it’s crucial to foster a reliable IT infrastructure. This article explores innovative strategies to empower remote teams, making collaboration a breeze, and helping businesses thrive. So, buckle up and discover the wonders of impeccable IT support in the virtual realm!
In the intricate dance between cybersecurity and data protection, access control audit and compliance steps forward as the key to harmony. By employing best practices, organizations can fortify their defenses and ensure the confidentiality, integrity, and availability of their precious digital assets. Dive into the world of access control audit and compliance to unleash the secret to safeguarding your data kingdom.
In the vast digital landscape, where predators lurk in every corner, network security protocols act as unwavering guardians. Imagine SSL as an impenetrable fortress, securing your online transactions, while VPNs cloak your identity, whisking you away to a hidden haven. Together, these technological marvels safeguard our interconnected world, ensuring a virtuous dance between convenience and protection. Let us delve deeper into these enigmatic enforcers, unraveling their secrets and revealing the essence of network security.
In today’s uncertain business landscape, cloud solutions have become an invaluable tool for ensuring smooth business continuity. Offering secure data storage, instant access to information, and seamless collaboration, the cloud enables organizations to swiftly adapt to any disruptions. Whether it’s a natural disaster or a cyberattack, cloud solutions provide the stability and flexibility needed to keep operations running seamlessly. Embracing the cloud is no longer a luxury but a necessity for businesses of all sizes looking to safeguard their future.
Imagine a world where dial tones are replaced by crystal-clear voices echoing through the internet. But is VoIP really the futuristic knight in shining armor for businesses, or does the reliability of traditional phone systems still hold its ground? Let’s explore the battle of the century between VoIP and traditional phone systems to help you make the right choice for your communication needs.
In today’s interconnected world, the need for seamless collaboration across departments has become imperative. Enter cloud integration – the ultimate solution that transcends boundaries, fostering a harmonious ecosystem where ideas flow effortlessly. Embrace the power of the cloud, and witness how it unifies teams, unlocks innovation, and propels your organization towards unprecedented success.
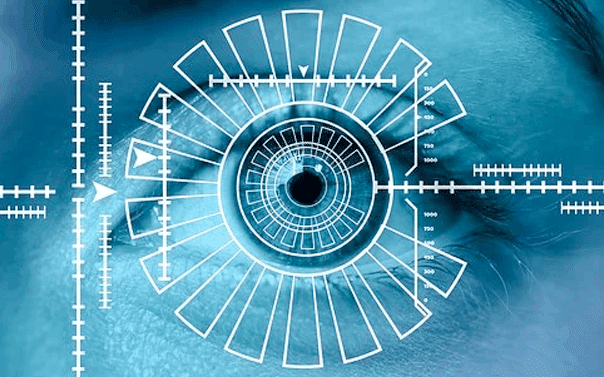
In a digital age where cyber threats loom large, safeguarding your business is paramount. That’s where robust access control systems come into play – the ultimate armor for your organization. From biometric authentication to smart card readers, these cutting-edge solutions fortify your perimeter, deterring unauthorized access and ensuring only the right people enter. Stay one step ahead in the realm of security and keep your business safe with an impenetrable fortress that leaves no room for compromise.
Access Control in the Age of IoT: Challenges and Solutions
In this interconnected world, the Internet of Things poses unique challenges for access control. With countless devices connected to networks, securing data and protecting privacy becomes paramount. This article explores the hurdles faced and innovative solutions that promise to safeguard our digital lives in this era of IoT.
When it comes to IT support for non-profit organizations, conventional approaches fall short. These organizations require a delicate balance between cost-effectiveness and efficient technology solutions. In this article, we explore the unique considerations that IT professionals need to keep in mind when supporting non-profits, ensuring their vital work can continue seamlessly.

In the realm of virtual collaborations, VoIP for video conferencing and webinars is gaining immense popularity. This innovative technology enables seamless and efficient communication, eliminating geographical barriers. An exploration into VoIP unveils a world of endless possibilities, where crystal-clear video and audio quality, interactive features, and cost-effective solutions take center stage. Join us as we embark on a creative journey into the realm of virtual connectivity, where VoIP leads the way.
In today’s rapidly evolving digital landscape, effective cloud integration is key for businesses to stay ahead of the competition. By seamlessly integrating cloud services into various business processes, companies can unlock a multitude of benefits – from improved operational efficiency to enhanced scalability. However, achieving successful cloud integration requires careful planning and adherence to best practices. In this article, we will explore some of the top strategies that businesses can implement to ensure smooth and efficient cloud integration in their day-to-day operations. So, let’s delve into the world of cloud integration and uncover the secrets to business success in the digital era.
In the ever-evolving digital era, data loss becomes a haunting reality for businesses and individuals alike. However, the silver lining lies in backup and recovery strategies, acting as the guardian angels of our precious files. But what makes these strategies foolproof? Join us on a journey as we unravel the secrets of preventing data loss and explore the technological wonders that ensure a smooth recovery.

In the fast-paced digital world, businesses need to adopt scalable solutions to keep up with rapid growth. Cloud technology is the answer! With its flexibility, unlimited storage, and seamless infrastructure, it allows businesses to effortlessly expand and adapt to changing demands. Embracing the cloud revolution is a surefire way to ensure long-term success and maximize business growth.
Title: Crafting a Safer Tomorrow: Evolution of Access Control in Manufacturing Facilities
As the sun slowly rises over the manufacturing landscape, a quiet transformation takes place. Gone are the clunky lock-and-key mechanisms, replaced by a symphony of cutting-edge access control systems. Innovations in safety and security have become the cornerstone of manufacturing facilities, ensuring a seamless blend of efficiency and confidentiality. In this article, we explore the vital role of access control in modern factory ecosystems, unveiling a vivid tapestry of safeguards that promise a brighter future.
In the ever-evolving world of business, cloud integration for customer relationship management (CRM) is a game-changer. The seamless connection between cloud solutions and CRM software empowers companies to deliver personalized experiences, boost productivity, and enhance customer satisfaction. Dive into the innovative realm of cloud integration and unlock the full potential of your CRM system.

In today’s fast-paced digital world, cloud-based project collaboration and management tools have become indispensable. These innovative platforms offer teams the ability to seamlessly connect, communicate, and coordinate tasks in real-time. With features like file sharing, task tracking, and centralized document management, these tools foster collaboration and streamline project workflows. From startups to large enterprises, cloud-based project collaboration and management tools have revolutionized the way teams work, bringing efficiency and agility to the forefront of business operations.
As the world becomes increasingly digital, organizations worldwide are embracing remote work. However, ensuring the security of remote workforces is paramount. Enter VPN and remote access solutions – the heroes of connectivity and data protection. Let’s dive into how these technologies safeguard businesses and their employees while unleashing the potential of remote work.
In the digital realm, lurking behind the invisible walls of networks, there exists a host of sinister threats, like shadowy specters craving to exploit vulnerabilities. From malware to phishing scams, daily we face countless perils. But fear not, as valiant defenders, armed with knowledge, rise to vanquish these foes. This article illuminates the treacherous landscape of network security threats and unveils potent remedies to safeguard your digital fortress. Brace yourselves for a journey through the shadows, where knowledge manifests as the greatest weapon for defenders of the cyber realm.
In a digital era where password leaks and cyberattacks are rampant, one needs more than just a password to secure their online presence. Two-factor authentication emerges as a commendable defense mechanism, ensuring an added layer of protection. By combining something you know (password) with something you have (a physical device), this dynamic duo fortifies access control like never before. It’s time to bid farewell to single-factor authentication and embrace this innovative shield to keep your online life out of harm’s way.

In a world where threats are ever-evolving, video surveillance has emerged as a critical tool in enhancing physical security. As the watchful eyes capture every movement, it offers an unparalleled sense of protection. From deterring crime to providing crucial evidence, these cutting-edge systems are a silent yet powerful guardian, tirelessly safeguarding lives and assets. With the advancement of technology, video surveillance ensures an unwavering vigilance, turning any premise into an impregnable fortress.
In this ever-evolving digital era, securing our cyber existence poses unprecedented challenges. The digital age’s common security issues continue to mount, transforming the online world into a potential battleground. From data breaches to identity theft, this article dives into the intricate web of security challenges we confront daily, highlighting the urgent need for robust online defense mechanisms.
In today’s digital age, communication and collaboration have become paramount for businesses to thrive. VoIP technology is revolutionizing the game by seamlessly integrating messaging and collaboration tools, creating a unified communications ecosystem. Discover how this enchanting pairing brings efficiency and productivity to your fingertips, fostering a truly connected workplace.
The world of VoIP protocols can be a maze of acronyms, but fear not! We are here to unravel the mysteries of SIP, RTP, and more. From signaling to media transmission, prepare to dive into the fascinating world of voice over IP. Join us on this journey of discovery, where technical terms become music to your ears!
In the ever-evolving world of communication, VoIP systems have become a game-changer. From classic IP telephony to unified communications, the options are seemingly endless. Dive into the realm of VoIP as we explore the fascinating array of systems that bring people closer, revolutionizing conversations with a stroke of digital magic.
Exploring the realm of VoIP security unveils the fortress of encryption and authentication. As the lifeblood of modern communication, Voice over Internet Protocol requires impenetrable protection. Prepare to delve into the fascinating world where advanced encryption algorithms guard your conversations, while robust authentication mechanisms verify identities. Together, they form an impregnable shield, ensuring your VoIP experience remains secure, reliable, and truly transformative.
In the realm of VoIP systems, the untold secret to seamless communication lies within the realm of voice quality and call optimization. A harmonious symphony of crystal-clear audio and efficient data transmission, these facets can make or break the user experience. This article delves into the intricacies of enhancing voice quality, tackling issues of latency, jitter, and packet loss, while exploring techniques to optimize call performance and ensure a symphony of voices that never misses a beat.
As the world continues to embrace remote work, the advantages of VoIP for remote workforces become increasingly evident. With seamless communication, affordable costs, and a wealth of features, VoIP allows remote workers to connect with colleagues and clients from anywhere in the world. Discover how this technology is transforming the way we work, promoting collaboration and productivity like never before.
In the vastness of the digital realm, countless clouds float, each offering a safe haven for your precious data. In this article, we embark on a journey to compare various cloud storage providers, decipher their hidden powers, and ultimately help you find the perfect one. Soar through the clouds with us to discover the ultimate storage solution for your digital universe.
Title: The Battle of Access Control: Biometric vs. Card-based Systems
Excerpt:
In the realm of access control, a fierce rivalry prevails as biometric and card-based systems go head-to-head. Like ancient gladiators, these technologies vie for supremacy, captivating the hearts of security enthusiasts worldwide. Each offers unique advantages, but which will triumph in this epoch-making bout? Let’s delve into the intricate world of access control and witness the clash of the titans.
In the dynamic world of sales, where every call counts, harnessing the power of VoIP is a game-changer. By seamlessly integrating CRM and call analytics, sales teams can unlock a treasure trove of valuable insights. From tracking customer interactions to analyzing call data, this innovative approach propels sales productivity and customer satisfaction to new heights. With VoIP revolutionizing the way businesses communicate, sales teams are well-equipped to make meaningful connections, drive sales growth, and triumph in the competitive marketplace.

In the seemingly boundless universe of technology, navigating through the complexities of IT systems can feel like an intergalactic voyage. Fear not, for the arrival of managed IT support brings a stellar solution. With its constellation of benefits, ranging from enhanced cybersecurity to efficient troubleshooting, businesses can now embark on a celestial journey towards streamlined operations and optimized productivity. Join us as we embark on a cosmic exploration of the manifold benefits bestowed upon organizations by managed IT support.

In a digital realm where information is omnipresent, ensuring data privacy remains a paramount concern for businesses leveraging the cloud. Delicate as petals, data privacy requires meticulous nurturing. This article unveils the best practices businesses need to adopt to safeguard their data in the cloud, shielding it from prying eyes. From encryption to access management, an armor of protection shall be woven to fortify your data’s sanctuary. Let us embark on this privacy odyssey together, embracing the cloud’s potential while safeguarding our most cherished asset – our data.
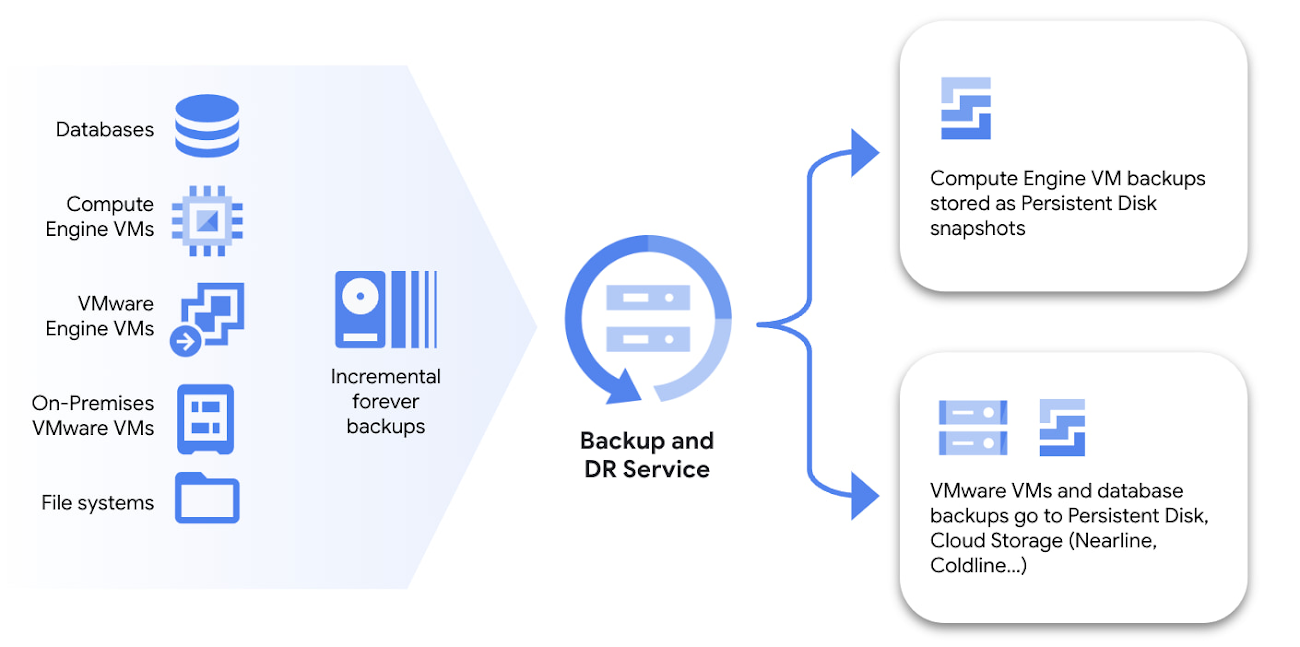
In a world where data is the new currency, businesses cannot afford to take risks with its safety. That’s where cloud solutions step in, offering a creative and efficient way to back up and recover essential information. By leveraging the power of the cloud, organizations can ensure seamless operations, minimal downtime, and enhanced data security. Whether it’s a natural disaster or an internal mistake, cloud solutions provide a neutral, reliable, and scalable option for data protection. It’s time to embrace the cloud and safeguard your business’s most valuable asset.
Access control is not just a mundane aspect of physical security; it is a formidable gatekeeper embodying both vigilance and protection. Like a symphony conductor, it orchestrates the harmony between safety and convenience, ensuring only authorized individuals pass through its hallowed gate. This guardian’s significance is often overlooked, but its presence is a testament to an organization’s commitment to safeguarding its assets and keeping its inhabitants secure.
In the ever-evolving realm of communication, VoIP call routing and call forwarding have emerged as game-changers. These innovative features not only streamline connectivity but offer endless possibilities. This article delves into the world of VoIP, uncovering the intricacies behind call routing and forwarding, illuminating how they reshape our modern conversations.
In today’s fast-paced business world, cloud integration has emerged as a game-changer. With its ability to streamline and simplify processes, it’s no wonder why more and more organizations are embracing this technology. From seamless data sharing to automated workflows, the cloud empowers businesses to work smarter, not harder. This article explores the various ways cloud integration can revolutionize your business processes, ultimately leading to increased productivity and growth. So, buckle up and get ready to explore the limitless possibilities of cloud integration!
In the ever-evolving world of technology, small businesses need a robust IT support system to thrive. But choosing the right one can be daunting. From budget limitations to scalability, this article explores the top considerations that small businesses must keep in mind to ensure they find the perfect IT support partner. Stay tuned for expert insights and valuable tips!
In an interconnected world, remote work has quickly become the norm. However, this new territory poses cybersecurity risks. Don’t fret! By following these best practices, you can fortify your digital fortress and stay safe amidst the virtual wilderness. Let’s dive in and decode the secrets of secure remote work!
In the ever-evolving world of project management, cloud-based solutions have become a game-changer. From seamless collaboration to real-time updates, these platforms offer a plethora of benefits. Let’s embark on a journey to explore the fascinating realm of cloud-based project management solutions and discover how they revolutionize the way teams work together. Get ready to witness a whole new level of efficiency and productivity!
In a world where every penny counts, businesses are constantly seeking innovative ways to cut costs. Enter VoIP, the money-saving superhero! With its cost-effective calling plans and efficient communication tools, VoIP can rescue your business from pricey traditional phone systems. Prepare for substantial savings and streamlined operations as VoIP swoops in to rescue your financial woes. Say goodbye to oversized phone bills and welcome a new era of cost-effective communication.
Faxing has come a long way since the days of bulky machines and paper jams. With the advent of Voice over Internet Protocol (VoIP) technology, virtual fax solutions offer a modern and efficient way to send and receive faxes. This article delves into the realm of VoIP faxing, exploring the benefits, features, and how businesses can harness this innovative solution to streamline their communication processes. Get ready to discover a world where traditional faxing meets the digital age!
As the guardians of public trust, government agencies must ensure foolproof access control policies and procedures to safeguard sensitive information. This article delves into the intricate world of access control, exploring dynamic strategies that empower agencies to maintain security without hindering functionality. Embark on this journey of policy and procedure exploration, as we unravel the secrets to effective access control in the realm of government. Get ready to fortify your agency’s defenses with creativity and precision.
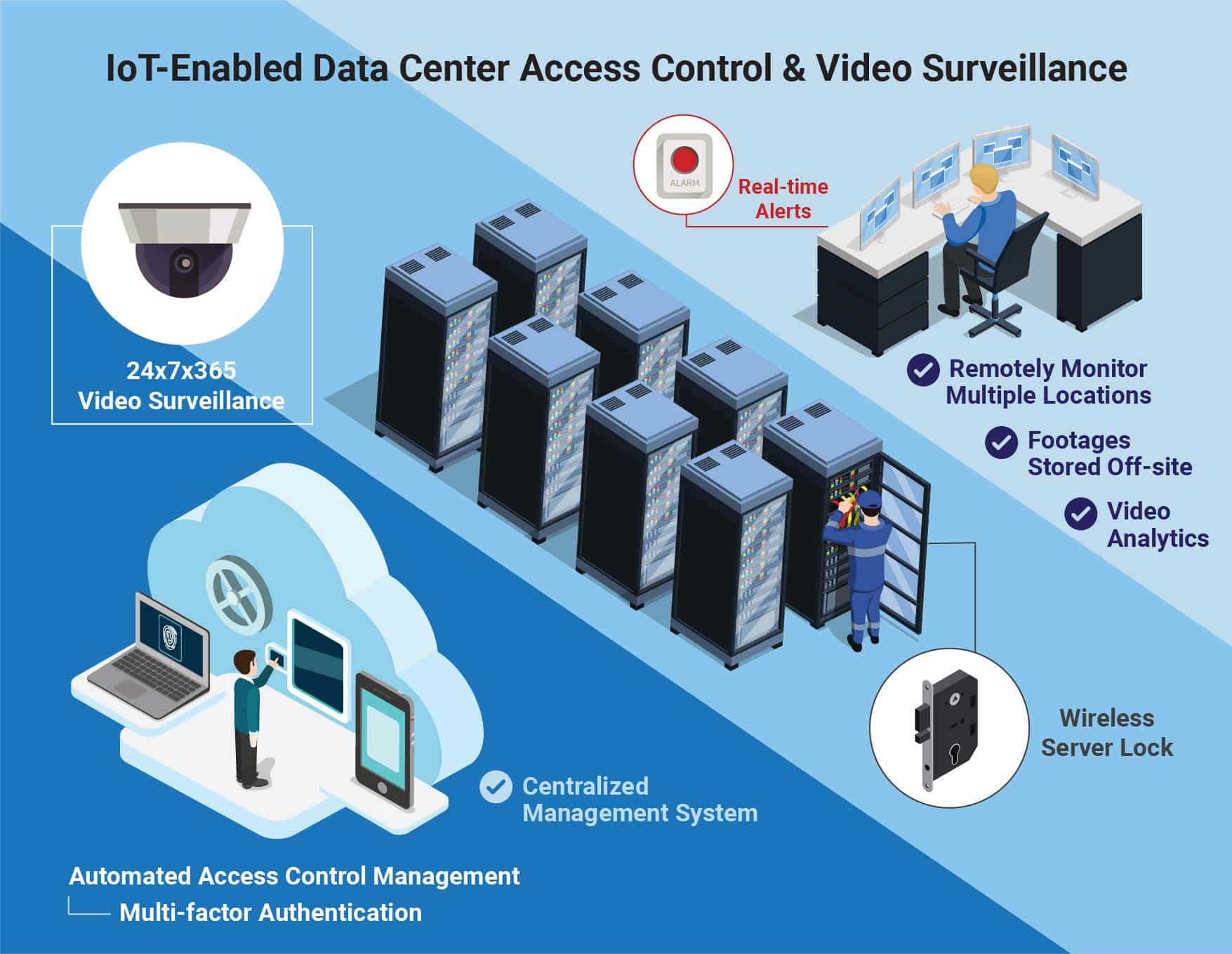
In the digital realm, where data reigns supreme, access control emerges as the indomitable guardian of the kingdom. Data centers and server rooms, housing a plethora of valuable information, demand robust measures to control accessibility. From biometric authentication to advanced keycard systems, the fortress of access control fortifies these sanctums from potential breaches. Let us delve into the world where the keys to the kingdom lie within the realm of advanced access control solutions.
Gone are the days of tedious bookkeeping and lengthy Excel spreadsheets. Enter the era of cloud-based accounting and financial management systems. These innovative solutions streamline processes, increase efficiency, and provide real-time access to crucial data. With the ability to securely store information and collaborate with team members, businesses of all sizes can enhance their financial management capabilities. Say goodbye to endless paperwork and embrace the simplicity of the cloud.
As technology advances at an unprecedented pace, the future of cloud integration seems boundless. With emerging trends like serverless architecture, AI-powered data synchronization, and blockchain-based security measures, businesses can anticipate a seamless and secure exchange of data between diverse cloud platforms. The integration landscape is evolving rapidly, promising enhanced efficiency, scalability, and cost-effectiveness. As we peer into the future, the possibilities for cloud integration seem limitless, transforming the way businesses operate and collaborate.
In the realm of customer service, effective communication is vital. VoIP, a cutting-edge technology, offers a creative solution to enhance communication channels. With its seamless integration and cost-effectiveness, businesses can now provide top-notch customer support, improving satisfaction and loyalty. Embracing VoIP is a game changer for those aspiring to take their customer service to new heights.

In this digital age, communication technology continues to evolve, leaving us spoilt for choice. But when it comes to VoIP, selecting the right hardware can be daunting. Do you go for IP phones or gateways? Let’s embark on a journey of exploration, delving into the world of voice over IP hardware and discover the perfect solution for your communication needs.
In the vast landscape of IT support, artificial intelligence has emerged as an adept guide to troubleshoot and resolve technical issues. With its uncanny ability to learn, adapt, and analyze vast amounts of data, AI streamlines support processes, minimizes downtime, and enhances the overall user experience. As technology evolves, AI continues to redefine the role of IT support, promising an exciting future where efficiency meets innovation.

In the ever-evolving landscape of data privacy and compliance, legal firms face immense challenges. But fear not, as IT support comes to the rescue! With their innovative solutions and unwavering commitment to secure data, legal firms can now navigate the intricate maze of regulations while focusing on what they do best – delivering justice. So, let’s dive into the realm of IT support for legal firms and unlock the secrets to a compliant and privacy-driven future.
In today’s digital era, businesses are constantly seeking ways to streamline operations and maximize efficiency. Outsourcing IT support services has emerged as a game-changing solution. From cost savings to access to specialized expertise, the benefits are aplenty. It’s time to embrace the power of outsourcing and unlock a world of possibilities for your business.
In the vast digital landscape, where networks act as lifelines, the role of IT support in network infrastructure design is paramount. Operating behind the scenes, these unsung heroes bring dreams to life, ensuring seamless connectivity, robust security, and optimal performance. With meticulous planning and a sprinkle of innovation, they craft the architectural wonders that power our interconnected world. Their expertise in hardware, software, and evolving technologies creates a sturdy foundation, enabling businesses to flourish and individuals to thrive in this ever-evolving digital age. As network infrastructure architects, IT support professionals truly shape the future.

The swirling clouds of technology continue to shape the future of business operations. From increased data processing capabilities to enhanced collaboration, cloud computing is set to revolutionize industries. With cloud adoption expanding rapidly, businesses are left with one question: how can they fully leverage this paradigm shift to stay ahead in the ever-evolving digital landscape? In this article, we delve into the future of cloud computing and its profound impact on businesses, exploring the potential benefits and risks associated with this transformative technology. Get ready to soar through the clouds as we explore the limitless possibilities that lie ahead.

In today’s digital world, protecting your business from cyber threats is paramount. Enhancing cybersecurity should be your top priority, as it ensures the safety of your sensitive data and preserves your reputation. This article explores effective tactics and strategies to fortify your defenses, empowering you to navigate the intricacies of the online landscape with confidence and resilience. Stay ahead of hackers, safeguard your business, and embrace a secure future!
In today’s fast-paced, globalized world, supply chain management is a critical aspect of any successful business. And with the advent of cloud integration, this task has become more efficient and streamlined than ever before. The cloud allows for seamless connectivity and real-time data sharing between suppliers, manufacturers, and distributors. It offers a unified platform where all stakeholders can collaborate, track inventory, and monitor shipments, ensuring a smooth and transparent flow of goods. With cloud integration, supply chain management has entered a new era of effectiveness, enabling businesses to adapt and thrive in the dynamic marketplace.
In today’s interconnected world, international teams are becoming the norm. However, communication can often be hindered by language barriers. Enter VoIP, the superhero of cross-cultural collaboration. With its advanced translation capabilities and seamless integration, VoIP is breaking down language barriers and connecting global teams like never before. Say goodbye to miscommunication and hello to a world of clarity and collaboration. VoIP is truly the bridge that unites us all.
As business owners, ensuring the safety and security of our premises is crucial. But with so many access control systems available, the task of choosing the right one can seem daunting. Fear not! This article will guide you through the process, helping you select an access control system that seamlessly blends innovation, affordability, and adaptability tailored to your business needs. So let’s explore the world of access control systems and pave the way for a secure future!
Apple has once again proved its commitment to inclusivity by announcing new accessibility features. Live Speech allows real-time captioning, while Personal Voice enables users to experience Siri in their own voice. These groundbreaking additions ensure a world where technology is accessible to all.
Twitter is about to bid farewell to its Head of Brand Safety and Ad Quality as they make an exit from the company. It remains to be seen what impact this departure will have on the social media giant’s advertising strategy. Stay tuned for more details as the story unfolds.
Apple Watch users have something exciting to look forward to with the launch of watchOS 10. Boasting an array of impressive features including widgets, new watch faces, and even mental health tracking, this update takes smartwatches to the next level. Get ready to personalize your watch and stay in tune with your overall well-being like never before.
In the fierce African marketplace, a Tiger Global-backed start-up is boldly entering the super-app race, aiming to revolutionize the way the continent engages online. With an innovative blend of services and a user-friendly interface, this promising venture may soon become the go-to app for millions across Africa. Stay tuned as this exciting saga unfolds!
In a remarkable triumph for space tourism, Virgin Galactic made history today as their commercial rocket plane soared beyond Earth’s atmosphere. Marking a new era for explorers, this momentous flight opens the door to boundless possibilities, igniting imaginations and making space exploration a tangible reality for everyday dreamers. A remarkable achievement that will undoubtedly leave an indelible mark on the pages of history.
In a world where technology giants are often embroiled in patent wars, Nokia and Apple have chosen a different path. With an innovative and collaborative spirit, the two tech giants have once again renewed their patents deal, marking a continuation of their fruitful partnership. This move not only ensures a steady stream of revenue for Nokia but also affirms the significance of cooperation in the ever-evolving tech landscape.
As the world increasingly shifts towards sustainable mobility, the South African market is proving itself ready to embrace electric vehicles (EVs). Greg Maruszewski, Managing Director of TCS | Volvo Cars, believes that the time is ripe for EV revolution in South Africa, highlighting the growing infrastructure and the country’s commitment towards reducing carbon emissions. With an optimistic outlook, Maruszewski believes that EVs will not only reduce our carbon footprint, but also revolutionize the way we commute, making us more connected to a greener future.
In a bid to embrace sustainability and broaden their electric vehicle range, BMW has announced plans to manufacture plug-in hybrids in South Africa. This bold move not only signifies the German automaker’s commitment towards eco-friendly solutions, but also boosts the country’s auto industry. South African car enthusiasts can look forward to experiencing BMW’s cutting-edge technology, seamlessly blending performance and eco-consciousness. A win-win for both the environment and the automotive sector.
In a sensational turn of events, Apple Inc. has rewritten the record books by surpassing a staggering $3-trillion valuation. With unwavering consumer loyalty and visionary innovation, the tech giant solidifies its throne in the corporate world. Having achieved this milestone, Apple continues to inspire awe and uphold its iconic status as the pinnacle of success in the realm of technology.
MTN, the leading telecommunications giant, has recently inked a groundbreaking deal with Meta, paving the way for zero-rated Facebook access in select regions. This unprecedented move seeks to bridge the digital divide, allowing users to explore the world’s largest social media platform without cost restraints. With this strategic partnership, MTN is poised to revolutionize connectivity, fostering digital inclusivity on an unprecedented scale.
In a twist of fate, OpenAI’s revolutionary ChatGPT model has landed the organization in the midst of a legal battle. Several authors are suing, claiming that the AI’s responses infringe upon their copyrighted work. The pioneering technology now faces the ultimate test – can artificial intelligence truly replicate the creativity of human authors, or is it stepping over the boundaries of intellectual property law?
Last updated: 27 February 2026
These Terms of Service (“Terms”) apply to (a) your use of the Nexus-UK-Hub website, portals, accounts, and online tools (the “Site”), and (b) all services we supply to you (the “Services”), including (without limitation) IT support, managed services, troubleshooting, installations, maintenance, remote support, onsite support, consultancy, cloud services, network and cybersecurity services, vulnerability and hardening work, firewall/router configuration, endpoint security assistance, CCTV/IP camera supply/installation/configuration/support, access control and monitoring-related configuration, smart home and IoT device installation/configuration/support, and any related products and Deliverables.
By using the Site or purchasing/using our Services, you agree to these Terms. If you do not agree, do not use the Site or Services.
1) About Us
Company name: Nexus-UK Ltd
Registered address: 83 Langbrook Road, London, England, SE3 8QZ
Trading address: Mayfield Road, Biddulph, Stoke-on-Trent, ST8 6LU
Company number: 16958629
VAT number: N/A
Email: uk@e-mail.nexus
Phone: +447782133272
Primary contact: Support Team
We provide our terms in a way that can be stored and reproduced, as required for online contracting.
3.1 Quotes are valid for [30] days unless stated otherwise.
3.2 A contract forms when we accept your Order in writing (including email), start providing Services, or you pay an invoice (whichever happens first).
3.3 If there is a conflict, the order of priority is: (1) SOW/Order, (2) any SLA, (3) these Terms, (4) proposal/quote, unless we expressly state otherwise.
4.1 We will provide the Services described in the relevant Order.
4.2 Timescales are estimates unless expressly agreed as binding in writing.
4.3 Changes to scope, requirements, site conditions, device choices, or assumptions may require a change to fees and/or timelines. We will inform you and, where appropriate, agree changes in writing before continuing.
4.4 We may provide Services remotely and/or onsite, depending on the Order. On-site delivery requires access, safe working conditions, and compliance with any building/site rules.
4.5 Where the Services involve cybersecurity, CCTV, or smart home/IoT systems, you acknowledge that performance and reliability may depend on third-party networks, firmware, vendor services, and your premises’ conditions (Wi-Fi coverage, cabling routes, power, interference, building materials, etc.).
5.1 You must provide timely and accurate information, instructions, and access (including admin credentials/permissions where needed) to allow us to deliver the Services.
5.2 You are responsible for maintaining adequate backups unless the Order states we are responsible. If you request work without an up-to-date backup, you accept the risk of data loss.
5.3 You must ensure you have all necessary rights, licences, consents, and permissions to provide Client Data and to allow us to access, troubleshoot, and modify systems as required for the Services.
5.4 You must ensure any premises work areas are safe, accessible, and suitable (including sufficient power, clear access to equipment, and safe ladder/loft access if required).
5.5 You are responsible for your internet connection and internal wiring/cabling unless the Order states we supply/modify it.
5.6 You must use our advice and Deliverables responsibly. If you choose not to follow security or stability recommendations, you accept increased risk.
5.7 Where delays or additional work arise due to your actions/omissions (including late responses, incomplete information, lack of access, or third-party delays outside our control), we may adjust timelines and charge additional fees at our standard rates.
6.1 You must not request or use the Services for unlawful activity, including any form of unauthorised access, interception, surveillance, or monitoring.
6.2 You confirm you own or have explicit authority to administer any systems, networks, accounts, devices, properties, or CCTV Systems we work on.
6.3 We will refuse requests that we reasonably believe are unlawful or would facilitate wrongdoing, including (without limitation) hacking, credential theft, covert surveillance, or installing/using cameras in ways that are illegal or violate others’ rights.
6.4 You are responsible for ensuring your own use of CCTV Systems complies with applicable law and guidance, including appropriate signage/notice where required, and respecting neighbours/third parties.
7.1 You must keep account credentials confidential and use reasonable security measures (strong passwords, MFA where available, secure devices).
7.2 You must notify us promptly if you suspect unauthorised access, compromise, or a security incident affecting systems relevant to the Services.
7.3 You must not use the Site or Services to:
(a) break the law or facilitate unlawful activity;
(b) distribute malware, conduct phishing, or attempt unauthorised access;
(c) interfere with or disrupt networks/systems;
(d) infringe intellectual property rights; or
(e) upload/transmit content you do not have the right to use.
7.4 We may suspend access to the Site/Services where reasonably necessary to protect systems, Client Data, our other clients, or to comply with legal/regulatory requirements.
8.1 Fees are as stated in the Order and are exclusive of VAT unless stated otherwise.
8.2 Invoicing will be as stated in the Order (e.g., upfront, monthly in advance, monthly in arrears, or milestone/time-and-materials).
8.3 Payment terms are 15 days from invoice date unless stated otherwise.
8.4 Unless expressly included in an Order/support plan, Services are provided on a time-and-materials basis at our standard rates, and any additional work requested outside scope will be chargeable.
8.5 If payment is overdue, we may (a) charge reasonable interest and recovery costs as permitted by law, and/or (b) suspend Services until payment is received.
8.6 You are responsible for all charges from third-party providers you choose or instruct us to use (e.g., cloud storage for recordings, camera subscription plans, broadband, SIM/data plans, domains, licences), unless the Order states we supply them.
9.1 If we supply hardware (including cameras, NVR/DVRs, routers, switches, sensors, hubs, smart locks, doorbells, or other IoT devices), ownership transfers to you once paid in full.
9.2 Unless the Order states otherwise, manufacturer warranties apply to hardware, and you may need to deal with the manufacturer for warranty claims; we can assist and may charge for time if not included in your plan.
9.3 We are not responsible for vendor decisions, discontinued features, forced firmware updates, app changes, cloud service shutdowns, or subscription requirement changes.
9.4 Compatibility depends on your environment and third-party platforms. We will use reasonable efforts to configure systems, but we cannot guarantee ongoing compatibility where third parties change their systems.
10.1 Placement and coverage: You are responsible for approving camera placement, fields of view, and recording settings. Environmental factors (lighting, glare, weather, obstructions, distance) affect image quality and detection performance.
10.2 Retention and storage: Recording retention depends on storage size, resolution/bitrate, motion settings, and cloud plan limits. Unless the Order states otherwise, you are responsible for selecting retention requirements and ensuring adequate storage.
10.3 Privacy settings: You are responsible for configuring and using privacy features (masking, zones, motion areas, audio recording settings) in accordance with your legal obligations.
10.4 Smart home reliability: Smart home/IoT devices may fail due to Wi-Fi coverage, interference, ISP outages, vendor outages, or firmware updates. Automation routines may be disrupted by third-party changes.
10.5 Critical systems: CCTV and smart home/IoT are not a guaranteed substitute for a monitored alarm service, emergency response service, or life-safety system unless expressly stated in the Order. You should not rely on them as the sole measure for safety-critical use.
11.1 Some Services depend on third-party networks and platforms (e.g., Microsoft, Google, ISPs, hosting providers, camera vendors, cloud recording providers, app stores, payment processors). Third-party terms and acceptable use policies may apply.
11.2 We are not responsible for third-party outages, discontinuations, price changes, or policy changes, but we will reasonably assist you with escalation and workarounds where appropriate.
11.3 We may use subcontractors to deliver parts of the Services. We remain responsible for our contractual obligations, subject to these Terms.
12.1 Support hours, response targets, and service levels (if any) are stated in the Order/support plan/SLA.
12.2 If no SLA is stated, support is provided on a reasonable endeavours basis during Mon–Fri 09:00–17:30 UK time, excluding public holidays. If you have purchased a 24/7 support service, the support hours and response targets will be as stated in your Order/support plan/SLA.
12.3 Planned maintenance may be required. We will use reasonable efforts to schedule maintenance to minimise disruption and to provide notice where feasible.
12.4 Emergency work outside support hours may be chargeable at enhanced rates unless included in your plan.
13.1 Each party retains ownership of intellectual property it owned before the contract.
13.2 Unless the Order states otherwise, upon full payment, we grant you a non-exclusive, non-transferable licence to use the Deliverables for your own internal or business purposes.
13.3 Deliverables may include third-party components and/or open-source software, which are licensed under their own terms. You agree to comply with those terms.
13.4 We retain all rights in our tools, scripts, templates, know-how, processes, and generic improvements developed during delivery, provided we do not disclose your confidential information.
14.1 Each party will keep the other’s Confidential Information confidential and will only use it to perform its obligations and exercise its rights under these Terms.
14.2 Confidentiality obligations do not apply to information that: (a) is or becomes public other than through breach; (b) was lawfully known before disclosure; (c) is independently developed without reference to the Confidential Information; or (d) must be disclosed by law, court order, or regulator (in which case the disclosing party will be notified where lawful and practicable).
15.1 Each party will comply with applicable data protection law, including the UK GDPR and the Data Protection Act 2018.
15.2 Where we process Personal Data on your behalf in providing the Services, and you determine the purposes and means of processing, you are the Controlle,r and we are the Processor.
15.3 We will process Personal Data only on your documented instructions, unless required to do otherwise by law.
15.4 We will implement appropriate technical and organisational measures to protect Personal Data against unauthorised or unlawful processing and against accidental loss, destruction, or damage.
15.5 We may use sub-processors (for example, hosting, ticketing, monitoring, remote support, cloud storage, CCTV cloud providers). Where required, we will ensure appropriate contractual protections are in place with sub-processors.
15.6 If Personal Data is transferred outside the UK, we will use lawful transfer safeguards where required.
15.7 We will notify you without undue delay after becoming aware of a Personal Data breach relating to processing we perform for you and will provide reasonable information to support your compliance obligations.
15.8 We will reasonably assist you (at your cost where appropriate) with responding to data subject rights requests and regulatory enquiries relating to our processing of Personal Data on your behalf, taking into account the nature of the processing and information available to us.
15.9 We will, at the end of the Services (or upon your written request), return or delete Personal Data processed on your behalf, unless retention is required by law or for legitimate purposes such as dispute resolution, security logging, or compliance.
15.10 Our processing of Personal Data for our own purposes (such as account management, billing, and marketing where permitted) is described in our Privacy Policy: See Page Footer. Our cookie practices are described in our Cookie Policy: See Page Footer.
16.1 We use cookies and similar technologies on the Site. Where required by law, we will request your consent before placing non-essential cookies on your device.
16.2 You can manage cookies via our cookie banner/settings and your browser controls.
16.3 We will only send direct marketing messages where we have a lawful basis to do so, and you can opt out at any time using the unsubscribe method provided or by contacting us.
17.1 If you are a Consumer, we will supply the Services with reasonable care and skill, and you have legal rights in relation to the Services and digital content supplied.
17.2 If you purchase Services at a distance (for example, online, by email, or by phone), you may have a legal right to cancel within 14 days from contract formation under the Consumer Contracts Regulations, unless an exception applies. If you ask us to begin Services during the cancellation period, you may be required to pay for Services provided up to the cancellation date, and you may lose the right to cancel once the Services are fully performed.
17.3 Nothing in these Terms affects your statutory rights.
18.1 We will perform the Services with reasonable care and skill.
18.2 Unless expressly stated in the Order, we do not warrant that the Services will be uninterrupted, error-free, or completely secure.
18.3 Cybersecurity reduces risk; it does not eliminate it. You acknowledge that even with appropriate controls, breaches and incidents can still occur due to evolving threats and third-party vulnerabilities.
19.1 Nothing in these Terms limits or excludes liability for:
(a) death or personal injury caused by negligence;
(b) fraud or fraudulent misrepresentation; or
(c) any other liability that cannot lawfully be limited or excluded.
19.2 Subject to clause 19.1, we are not liable for:
(a) indirect or consequential loss;
(b) loss of profits, revenue, business, goodwill, anticipated savings, or opportunity;
(c) loss, corruption, or compromise of data where you have not maintained adequate backups and/or where such loss arises from factors outside our reasonable control;
(d) failures caused by third-party services, networks, cloud platforms, camera vendor services, app platforms, power issues, ISP outages, or supplier changes, except to the extent directly caused by our breach of these Terms;
(e) missed events/incidents where detection, recording, notifications, or monitoring are impacted by environmental factors, configuration choices approved by you, storage limitations, connectivity, or third-party outages.
19.3 Subject to clause 19.1, our total aggregate liability to you (whether in contract, tort (including negligence), breach of statutory duty, or otherwise) arising out of or in connection with the Site and/or Services will not exceed:
(a) If you are a Consumer: the greater of (i) £5,000 and (ii) 100% of the fees paid and payable by you to us in the 12 months immediately preceding the event giving rise to the claim; and
(b) If you are a registered business customer (including an SME): the greater of (i) £10,000 and (ii) 125% of the fees paid and payable by you to us in the 12 months immediately preceding the event giving rise to the claim.
19.4 We will not be liable for security incidents or unauthorised access where the cause is attributable to (a) your failure to implement reasonable security measures, (b) your failure to follow our reasonable recommendations, (c) compromised credentials not caused by our breach, (d) insecure devices you choose to deploy against our advice, or (e) vulnerabilities or failures in third-party systems outside our reasonable control.
19.5 Where you are a business client, the limitations and exclusions in these Terms apply to the maximum extent permitted by law and are intended to be reasonable under the Unfair Contract Terms Act 1977.
You will indemnify and keep indemnified Nexus-UK-Hub against losses, damages, costs, and expenses (including reasonable legal fees) arising from third-party claims relating to:
(a) your unlawful use of the Site/Services;
(b) your breach of these Terms; or
(c) Client Data or materials you provide infringing third-party rights, including claims arising from unlawful camera placement or unlawful monitoring carried out by you.
21.1 Either party may terminate an Order/SOW by written notice if the other party commits a material breach and fails to remedy that breach within 14 days of being asked in writing to do so.
21.2 Either party may terminate immediately by written notice if the other party becomes insolvent, enters administration/liquidation, or is otherwise unable to pay its debts as they fall due.
21.3 We may suspend Services immediately on written notice if: (a) invoices are overdue, (b) we reasonably believe continued delivery would create a security or legal/compliance risk, or (c) your use of the Site/Services breaches clause 6 or 7.
21.4 On termination or expiry:
(a) You must pay all outstanding invoices and fees for Services performed up to the termination date;
(b) Any licences granted end if you have not paid all amounts due;
(c) We will return or delete Client Data as described in clause 15, subject to lawful retention and technical constraints;
(d) clauses intended to survive termination (including 13, 14, 15, 19, 20, 22, and 23) will survive.
Neither party is liable for any failure or delay caused by events beyond its reasonable control, including major internet/telecoms failures, widespread cloud outages, acts of government, natural disasters, industrial disputes, or other events that could not reasonably have been avoided. If such an event continues for more than 30 days, either party may terminate the affected Order by written notice.
If you have a complaint, contact complaints@e-mail.nexus with details. We will acknowledge within 2 Business Days and aim to propose a resolution promptly. Nothing in this clause prevents either party from seeking urgent injunctive relief where necessary.
We may update these Terms from time to time. The version posted on the Site will apply from the “Last updated” date. For ongoing support plans, if a change materially reduces your rights or increases your obligations, we will use reasonable efforts to notify you before it takes effect. Your continued use of the Site/Services after the effective date means you accept the updated Terms.
Notices must be in writing and may be sent by email to the email address last used for account/admin communications or to any other address stated in the Order. Notices are deemed received on the next Business Day after sending, provided no delivery failure notice is received.
26.1 Entire agreement: These Terms and the relevant Order/SOW form the entire agreement between the parties relating to their subject matter.
26.2 Severance: If any part of these Terms is found unenforceable, the remainder remains in force.
26.3 Assignment: You may not transfer or assign your rights/obligations without our prior written consent. We may assign these Terms to a successor in connection with a merger, acquisition, or sale of assets, provided this does not reduce your rights.
26.4 No waiver: A failure to enforce a term is not a waiver of that term.
26.5 Third party rights: No one other than you and us has any rights to enforce these Terms under the Contracts (Rights of Third Parties) Act 1999.
These Terms and any dispute arising out of or in connection with them are governed by the laws of England and Wales. The courts of England and Wales have exclusive jurisdiction, except that Consumers may bring claims in the courts of their place of residence in the UK where applicable law permits.
Last updated: 27 February 2026
This Privacy Policy explains how Nexus-UK (“we”, “us”, “our”) collects, uses, shares and protects personal data when you:
– visit our website and use our online services (the “Site”);
– contact us or request a quote;
– buy or receive our IT, cybersecurity, CCTV/IP camera, access/security-related, and smart home/IoT services (the “Services”);
– interact with us as a customer, supplier, partner or job applicant.
Company name: Nexus-UK Ltd
Registered address: 83 Langbrook Road, London, England, SE3 8QZ
Trading address: Mayfield Road, Biddulph, Stoke-on-Trent, ST8 6LU
Company number: 16958629
VAT number: N/A
Email: uk@e-mail.nexus
Phone: +447782133272
Primary contact: Support Team
We are usually the “controller” for personal data we collect for our own business purposes (e.g., running the Site, sales, billing, account management).
For many Services (especially managed IT/security services), we may also process personal data on behalf of a business customer. In those cases, the business customer is usually the controller and we act as a processor.
We may collect the following categories of personal data (depending on how you interact with us):
A. Site and communications
– Identity and contact details: name, email, phone number, address (if provided).
– Messages and enquiries: what you send us via forms, email, chat or phone.
– Technical and usage data: IP address, device type, browser type, pages viewed, date/time, referring pages, approximate location from IP.
– Cookie/consent preferences.
B. Customers and service delivery (IT/security/CCTV/smart home)
– Account and contract data: company name (if applicable), billing address, invoices, payment status, service plan, support history.
– Service and ticket data: support requests, notes, communications, work logs, device inventories, configurations.
– Network/security operational data: system logs, event logs, alerts, telemetry, patch status, vulnerability findings, firewall/router logs, endpoint security status, access/admin audit trails (where relevant to the Services and your instructions).
– Device identifiers: serial numbers, MAC addresses, hostnames, camera model IDs, hub IDs.
– Onsite visit data: appointment details, access instructions, job photos of equipment/installation (where necessary).
– CCTV-related data: we do not normally “own” your footage. However, if you ask us to configure, test, troubleshoot, or support your CCTV system, we may temporarily access or view live streams/recordings or related metadata (e.g., camera names, timestamps, motion events) to deliver support.
C. Payments
– We may receive limited payment data from our payment provider(s) (e.g., last 4 digits, transaction reference). We do not store full card details unless explicitly stated.
D. Recruitment (if applicable)
– CVs, employment history, references, and communications.
We use personal data to:
– Provide the Site and customer support.
– Respond to enquiries and provide quotes.
– Set up and deliver Services, including remote/onsite support, troubleshooting and maintenance.
– Manage accounts, contracts, billing, and payments.
– Improve and secure our Site and Services (including preventing fraud and misuse).
– Send service communications (e.g., outage notices, security advisories, changes to plans).
– Send marketing where permitted and in line with your preferences.
– Comply with legal and regulatory obligations and handle disputes.
We rely on one or more of these lawful bases (depending on the activity):
– Contract: to provide Services or take steps you request before entering a contract.
– Legitimate interests: to run our business, improve services, secure our systems, prevent fraud, and respond to enquiries (balanced against your rights).
– Legal obligation: to meet legal duties (e.g., tax/accounting).
– Consent: for certain cookies/analytics/marketing where required, and for some optional communications.
– Vital interests: rare, where necessary to protect someone’s life.
– Public task: rare, where applicable to a specific situation.
We do not aim to collect “special category data” (e.g., health, biometrics) as part of normal operations.
However, CCTV footage could incidentally capture sensitive information. Where we access any such data for support, we do so only as needed to deliver Services and in line with your instructions and applicable law.
We may share personal data with:
– Service providers we use to operate our business: hosting, email, ticketing/CRM, remote support tools, monitoring tools, accounting, document storage, analytics (where enabled), payment processors.
– Suppliers/contractors/subcontractors: where needed to deliver Services (e.g., cabling partners) under appropriate obligations.
– Third-party platforms you choose: e.g., Microsoft 365, Google, camera vendors, cloud recording providers, smart home platforms, ISPs.
– Authorities/regulators/law enforcement: where required by law or to protect rights and safety.
– Professional advisers: legal, insurance, accounting.
Some providers we use may process data outside the UK. Where required, we use appropriate safeguards for international transfers (such as adequacy regulations or approved contractual protections).
We keep personal data only for as long as needed for the purposes described above, including:
– Enquiries: typically up to 24 months after last contact.
– Contracts, billing and tax records: typically 6 years (or as required by law).
– Support tickets and service records: typically for the contract term plus 12–36 months.
– Security logs: typically 180 days unless longer retention is required for investigation, legal reasons, or contract terms.
– CCTV support access: we do not normally retain footage; if any screenshots/exports are created for troubleshooting, retention will be limited to what is necessary and agreed/needed (typically days or weeks, not forever).
Exact retention can vary depending on the Service and legal obligations.
Depending on the circumstances, you may have rights, including:
– Access to your personal data.
– Rectification of inaccurate data.
– Erasure (in some cases).
– Restriction of processing (in some cases).
– Objection to processing (especially where we rely on legitimate interests).
– Data portability (where applicable).
– Withdraw consent at any time where we rely on consent (this does not affect processing already carried out).
To exercise your rights, contact: privacy@e-mail.nexus / complaitns@e-mail.nexus
If you have concerns, please contact us first and we’ll try to resolve it.
You also have the right to complain to the UK Information Commissioner’s Office (ICO).
We use appropriate technical and organisational measures designed to protect personal data, such as access controls, least-privilege practices, encryption where appropriate, secure authentication, and monitoring.
If you operate CCTV or smart home/IoT systems, you are responsible for using them lawfully, including:
– having a valid reason for recording and monitoring;
– using signage/notice where required;
– configuring privacy features (masking, zones, audio settings) appropriately;
– handling access to footage and user accounts securely;
– responding to requests about footage where you are legally required to do so.
Where we provide installation/configuration/support, we do not decide why/how you use your system; you do. We may act as a processor where we access data on your behalf for support.
Our Services and Site are not intended for children. If you believe a child has provided us with personal data, contact us, and we will address it.
We may update this Privacy Policy from time to time. We will post the updated version on our Site with a new “Last updated” date.
Privacy queries: privacy@e-mail.nexus
General support: uk@e-mail.nexus
Last updated: 27 February 2026
This Cookie Policy explains how Nexus-UK-Hub (“we”, “us”, “our”) uses cookies and similar technologies on our website (the “Site”).
Cookies are small text files placed on your device when you visit a website. Similar technologies include pixels, tags, local storage, SDKs and other identifiers. These help websites work properly, improve functionality, and provide information about how the site is used.
We use cookies and similar technologies for:
– Strictly necessary purposes: to make the Site work, keep it secure, and enable core features.
– Preferences: to remember choices you make (where enabled).
– Analytics: to understand how the Site is used and improve it (only where enabled).
– Marketing: to measure marketing performance or show relevant content (only where enabled).
We use a cookie banner/consent tool to let you choose which non-essential cookies are used.
– Strictly necessary cookies do not require consent because they are required for the Site to function.
– Analytics and marketing cookies are used only if you consent (or where another lawful basis is permitted by law and implemented appropriately).
You can change your cookie choices at any time by:
– clicking [Cookie Settings] on the Site; and/or
– adjusting your browser settings to block or delete cookies.
The cookies on your Site will depend on which tools you enable (e.g., analytics, chat widgets, embedded video, booking tools).
A. Strictly Necessary Cookies (always on)
These are required for the Site to work and for security.
Examples:
– Session cookies for page navigation and basic site operations
– Security cookies (e.g., to help detect abuse)
– Consent-management cookie (to remember your choices)
B. Preference Cookies (optional)
These remember your settings (e.g., language or region) if you use those features.
C. Analytics Cookies (optional)
These help us understand how visitors use our Site (e.g., which pages are popular).
We only use these if you consent in our cookie banner.
D. Marketing Cookies (optional)
These may be used to measure advertising effectiveness or provide relevant content.
We only use these if you consent in our cookie banner.
Add your actual cookies here (your consent tool usually provides an export/list).
For each cookie include:
– Cookie name
– Provider/domain
– Purpose
– Category (Necessary/Preferences/Analytics/Marketing)
– Expiry
Example format:
Cookie Name: [cookie_name]
Provider: [yourdomain.com or vendor]
Purpose: [what it does]
Category: [Necessary/Preferences/Analytics/Marketing]
Expiry: [session / X days / X months]
If we embed third-party services (e.g., YouTube videos, maps, chat widgets, booking tools), those providers may set cookies when you interact with the embedded content. We will treat such cookies as non-essential unless they are strictly necessary, and where required, we will request your consent.
Most browsers allow you to:
– see what cookies are stored;
– delete cookies; and
– block cookies from specific sites or all sites.
Browser controls vary. Search your browser’s help pages for “cookies” to find the steps.
We may update this Cookie Policy from time to time. We will post the updated version on the Site with a new “Last updated” date.
If you have questions about our cookies:
Email: privacy@e-mail.nexus