In today’s fast-paced and ever-evolving digital landscape, businesses of all shapes and sizes are increasingly relying on information technology (IT) to streamline their operations. However, ensuring smooth IT operations and conquering complex technical challenges can often become overwhelming and time-consuming for internal teams. It is in this context that the concept of outsourcing IT support services emerges as a shining knight, offering a multitude of benefits to organizations. From alleviating the burden on internal resources to gaining access to specialized expertise, the advantages of outsourcing IT support services are as vast as the boundless horizons of the digital realm. In this article, we will delve into the dynamic world of outsourced IT support services and explore the marvelous advantages they bring to businesses across industries. So, fasten your seatbelts and get ready to unlock the transformative power of strategic outsourcing.
1. Boosting Efficiency and Productivity: How outsourced IT support services can maximize your company’s workflow
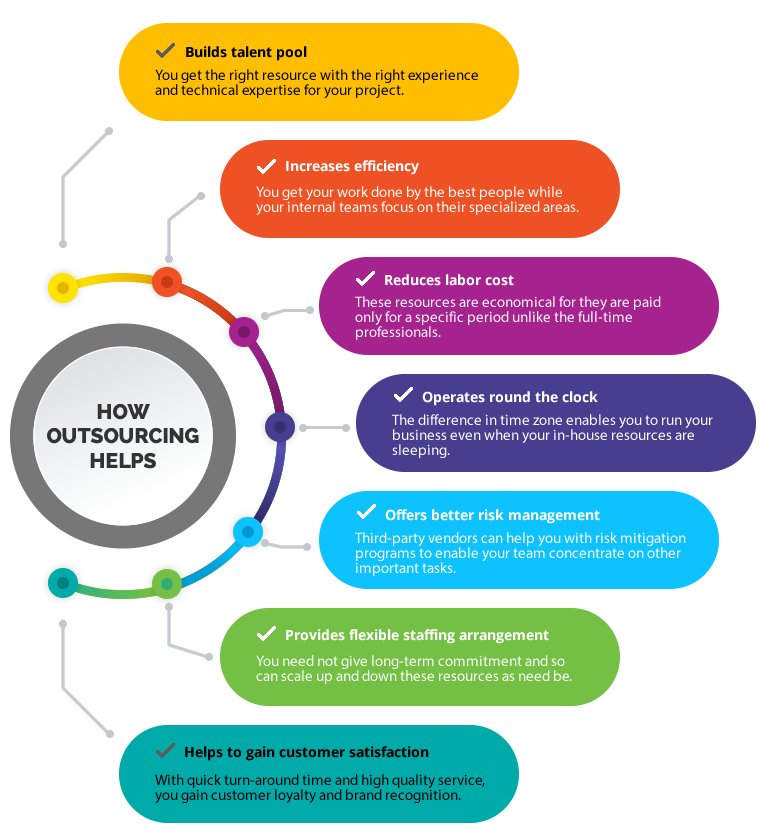
Outsourced IT support services have become a game-changer for businesses, enabling them to enhance efficiency and productivity in ways unimaginable before. By utilizing these services, companies can offload their IT-related tasks to professionals, freeing up valuable time and resources to focus on core business operations.
So how exactly can outsourced IT support services maximize your company’s workflow? Let’s dive into the key benefits:
- Expertise and Specialization: Outsourcing your IT support means gaining access to a team of experts who specialize in various areas of technology. These professionals possess the knowledge and experience needed to quickly resolve technical issues, implement upgrades, and provide proactive monitoring to prevent potential disruptions. With their skills and up-to-date industry insights, they ensure your company’s IT infrastructure is always optimized and running smoothly.
- Cost Reduction and Scalability: Maintaining an in-house IT team can be expensive, not to mention the ongoing costs of hardware, software, and licenses. Outsourced IT support allows you to reduce expenses significantly as you only pay for the services you need. As your company grows, these services can effortlessly scale to match your requirements, giving you the flexibility to adapt without the hassle of hiring and training additional staff. This cost-effective approach empowers your business to allocate resources more efficiently.
- Risk Mitigation and Security: Cybersecurity threats are a constant concern and can be devastating to a company’s workflow if not properly addressed. Outsourced IT support services prioritize security measures, implementing robust firewalls, data encryption, regular backups, and disaster recovery plans. They stay up-to-date with the latest security practices and regulations, mitigating risks and safeguarding your company’s sensitive information from potential breaches.
- 24/7 Support: Technical issues never seem to favor working hours. With outsourced IT support services, you have round-the-clock assistance. Whether it’s a midnight server crash or a weekend software glitch, experts are just a call away, ensuring minimal downtime and uninterrupted workflow for your company.
As businesses increasingly recognize the advantages of outsourced IT support, their workflow sees a significant boost in efficiency and productivity. By strategically utilizing the specialized expertise provided by external IT professionals, companies can navigate the complex technological landscape with ease while focusing on what they do best.
2. Cutting Costs and Resource Allocation: Unleashing the potential savings of outsourcing your IT support needs
When it comes to managing and maintaining your IT infrastructure, outsourcing your IT support needs can be a game-changer for your business. One of the most significant advantages of outsourcing is the potential cost savings it can bring. By entrusting your IT support to a specialized external provider, you can eliminate the need to invest in costly in-house IT staff, equipment, and infrastructure. This means you can redirect your resources and allocate them more efficiently towards other critical areas of your business.
Outsourcing your IT support needs also enables you to tap into the expertise and experience of professionals who specialize in the field. With a dedicated IT support team at your disposal, you can benefit from their in-depth knowledge of the latest technologies and industry best practices. This not only ensures that your IT issues are resolved efficiently and effectively but also allows you to stay ahead of the curve in terms of technological advancements.
- Cost savings through elimination of in-house IT staff, equipment, and infrastructure
- Redirected resources for better allocation towards core business functions
- Access to specialized expertise and experience in IT support
- Efficient and effective resolution of technical issues
- Stay up-to-date with the latest technologies and industry trends
By outsourcing your IT support needs, you can unleash the potential cost savings and resource allocation opportunities that were previously untapped. Not only does it allow you to streamline your operations and reduce overhead costs, but it also ensures that your IT infrastructure is in safe hands, backed by professionals who are dedicated to providing top-notch support.
Take the leap and explore the transformative benefits of outsourcing your IT support requirements today!
3. Unlocking Expertise: Harnessing the power of specialized knowledge by outsourcing IT support services
In today’s ever-evolving digital landscape, businesses struggle to keep up with the increasing demands of IT support. But fret not, as there is a solution! By harnessing the power of specialized knowledge and outsourcing IT support services, companies can unlock a world of expertise that can propel their business forward.
Outsourcing IT support services offers several advantages that can transform the way businesses operate. Let’s delve into some key benefits:
- Access to a specialized skill set: By outsourcing IT support, companies gain access to a pool of experts with specialized knowledge in various areas of technology. Whether it’s troubleshooting network issues, managing cybersecurity threats, or optimizing software infrastructure, these professionals have the expertise to handle any situation efficiently.
- Cost-effective solution: Building an in-house IT support team can be a costly endeavor. By outsourcing, businesses can save significantly on recruitment, training, and employee benefits. Additionally, it provides the flexibility to scale resources up or down as per the organization’s requirements, ensuring optimal cost management.
- Focused core competency: One of the biggest advantages of outsourcing IT support services is that it enables businesses to concentrate on their core competencies. By entrusting the complex task of IT management to experts, organizations can redirect their time, energy, and resources towards activities that directly impact their growth and success.
4. Streamlining Operations: How outsourced IT support services can improve your company’s overall efficiency
Outsourcing IT support services has emerged as a game-changer for businesses aiming to streamline their operations and boost overall efficiency. By entrusting your IT needs to a team of experts, you can unlock a whole new level of productivity. Here’s how:
1. Cost savings: Outsourcing IT support services helps you cut down on expenses associated with hiring, training, and retaining an in-house IT team. Instead, you can leverage the expertise of an outsourced provider at a fraction of the cost, allowing you to allocate financial resources to other critical areas of your business.
2. 24/7 support: Partnering with an outsourced IT support team provides you with uninterrupted assistance around the clock. Be it day or night, you can rely on their dependable support to troubleshoot issues promptly, minimizing downtime and ensuring smooth operations. This level of accessibility grants your business the flexibility to thrive in an always-on digital world.
5. Minimizing Downtime: The role of outsourced IT support services in ensuring uninterrupted business operations
In today’s fast-paced business environment, minimizing downtime is crucial for the success of any organization. With increasing reliance on technology, even a few minutes of downtime can result in significant financial losses and damage to a company’s reputation. Outsourced IT support services play a vital role in ensuring uninterrupted business operations by providing proactive maintenance, rapid troubleshooting, and effective problem resolution.
By outsourcing IT support, businesses can benefit from the expertise and dedicated resources of trained professionals who specialize in identifying and addressing potential issues before they escalate into major problems. Here are some key ways in which outsourced IT support services contribute to minimizing downtime:
- 24/7 Monitoring and Maintenance: Outsourced IT support teams constantly monitor your systems to identify any abnormalities or potential threats. This proactive approach allows them to address issues before they cause disruptions and ensures that your business operations run smoothly.
- Rapid Response and Troubleshooting: When unexpected IT issues occur, outsourced IT support services provide swift responses to minimize the impact on your business. Their expertise and experience enable them to quickly diagnose and resolve problems, keeping downtime to a minimum.
- Disaster Recovery Planning: Outsourced IT support teams develop comprehensive disaster recovery plans to ensure that your business can quickly recover from any unforeseen events such as natural disasters, cyber attacks, or hardware failures. These plans include regular data backups, redundant systems, and efficient recovery strategies to ensure uninterrupted operations.
- Managed Security Services: By outsourcing IT support, businesses can benefit from robust security measures that protect against potential threats and vulnerabilities. IT support teams implement and manage advanced security protocols such as firewalls, antivirus software, and employee training to safeguard your systems and data.
With outsourced IT support services, businesses can focus on their core operations, knowing that their systems are in capable hands. By minimizing downtime, these services contribute to increased productivity, improved customer satisfaction, and a competitive advantage in today’s dynamic business landscape.
6. Fostering Scalability and Flexibility: The advantages of outsourcing IT support services to accommodate your company’s growth
Outsourcing IT support services can greatly benefit your company’s growth by providing scalability and flexibility. This approach allows you to efficiently manage your resources and adapt to changes in demand without the need for significant investments in infrastructure or personnel. By outsourcing, you can take advantage of the following advantages:
- Access to a pool of expertise: By partnering with an IT support service provider, you gain access to a team of skilled professionals who specialize in various areas of technology. This allows your company to leverage their expertise and knowledge, ensuring that your IT systems are well-maintained and equipped to handle your expanding needs.
- Cost-efficiency: Outsourcing IT support services can help reduce costs associated with hiring and training an in-house IT team. Additionally, you can avoid expenses related to infrastructure and equipment upgrades as these responsibilities are shouldered by the service provider. This frees up valuable financial resources that can be allocated to other core business areas.
- Scalability: As your company grows, so do your IT requirements. Outsourcing IT support services offer the advantage of easily scaling up or down based on your changing needs. Whether it’s adding additional servers, expanding storage capacity, or increasing network bandwidth, a reliable service provider can swiftly adapt your IT infrastructure to accommodate your expanding business.
By outsourcing IT support services, your company gains the ability to grow and adapt with ease while minimizing the associated risks and costs. Whether you need to rapidly scale up during peak periods or streamline your IT operations during off-peak times, outsourcing provides the scalability and flexibility necessary to ensure your company’s continued success.
7. Enhancing Cybersecurity: The paramount importance of outsourced IT support services for protecting your digital assets
When it comes to protecting your valuable digital assets, outsourcing IT support services is an absolute must. In today’s interconnected world, cyber threats are constantly evolving and becoming more sophisticated. By enlisting the help of skilled professionals, you can ensure that your cybersecurity measures are up to par and that your business remains safe from potential attacks.
There are several key reasons why outsourced IT support services are paramount for enhancing cybersecurity:
- Expertise and Experience: IT support service providers specialize in cybersecurity and have a wealth of knowledge and experience in dealing with various threats. They stay updated with the latest trends and advancements in the field, ensuring that your digital assets are protected by the best practices.
- Advanced Tools and Technologies: Outsourced IT support services have access to state-of-the-art tools and technologies that are specifically designed to detect and mitigate cyber threats. These tools provide real-time monitoring, threat analysis, and rapid response capabilities to safeguard your digital infrastructure.
- Round-the-Clock Monitoring: Cyber threats can strike at any time, which is why it’s crucial to have 24/7 monitoring in place. IT support service providers offer continuous monitoring, ensuring that potential security breaches are detected and addressed promptly.
By leveraging outsourced IT support services, you can prioritize the protection of your digital assets and focus on what matters most – growing and running your business.
8. Access to State-of-the-Art Technology: How outsourcing IT support services can provide your business with cutting-edge tools
Outsourcing IT support services comes with a plethora of benefits, one of which is gaining access to state-of-the-art technology that can give your business a competitive edge in the market. With outsourcing, you no longer need to worry about investing in expensive software and hardware upgrades. Instead, you can rely on your service provider to equip your business with cutting-edge tools and technology. This allows you to stay up-to-date with the latest advancements without the hassle and cost of constantly upgrading your own infrastructure.
When you outsource IT support, you open the door to a wide range of advanced technologies that can streamline your operations and enhance productivity. From cloud computing solutions to data analytics tools, your service provider can offer you a vast array of options to choose from. By leveraging these resources, you can securely store and access your data, collaborate with team members effortlessly, and gain valuable insights through advanced analytics. You can also enjoy benefits like multi-factor authentication, data encryption, and disaster recovery systems that ensure the safety and integrity of your valuable business information.
9. 24/7 Support and Peace of Mind: Understanding the value of around-the-clock outsourced IT support services
When it comes to IT support services, having 24/7 support can bring an immense sense of peace of mind to businesses. With around-the-clock assistance, companies can rest assured knowing that any technical issues or inquiries will be promptly addressed, minimizing downtime and maximizing productivity. But what exactly is the value of this type of outsourced IT support? Let’s delve into some key aspects.
Timely Problem Resolution: One of the main benefits of 24/7 IT support is the ability to resolve problems swiftly. No matter the time of day or night, businesses can rely on a dedicated team to tackle any IT issues that may arise. This constant availability ensures that any disruptions to workflow are minimized, allowing operations to continue seamlessly.
Reduced Costs: Instead of hiring and maintaining an in-house IT team, outsourcing around-the-clock IT support can prove to be a cost-effective solution for many businesses. By partnering with a reliable service provider, companies can avoid the expenses associated with recruiting, training, and retaining a full-fledged IT department. Additionally, outsourced IT support often comes with predictable monthly costs, eliminating the need for unexpected expenses relating to infrastructure, software, or personnel.
10. Focus on Core Competencies: The freedom gained when outsourcing IT support services, allowing your team to concentrate on strategic goals
Outsourcing IT support services can be a game-changer for your business. By entrusting these important tasks to a dedicated team, you can free up your internal resources and allow your team to focus on what they do best: achieving strategic goals. This newfound freedom can have a significant impact on the overall success and growth of your organization.
By outsourcing IT support services, you can benefit from:
- Specialized Expertise: IT outsourcing companies have a deep pool of talented professionals who specialize in various areas. This means that your team can leverage their expertise to solve complex technical challenges without investing in costly training or hiring new staff.
- Increased Efficiency: With dedicated IT support, your employees can stop wasting valuable time resolving technical issues or maintaining systems. Instead, they can focus on core competencies that directly contribute to your business’s strategic goals, such as product development, market research, or client acquisition.
- Cost Savings: Outsourcing IT support removes the need for in-house infrastructure, equipment, and staff. This results in significant cost savings that can be redirected towards other critical business areas or invested in innovation and growth.
- Scalability: As your business expands, outsourced IT support allows you to quickly scale up or down based on your needs. Whether you need additional support during peak periods or want to adjust resources during slower times, an outsourcing partner can provide the flexibility you require.
By embracing the freedom gained through outsourcing IT support services, you can not only achieve operational efficiencies but also gain a competitive advantage in today’s dynamic business landscape.
In a fast-paced world driven by technology, the smooth functioning of your business often hinges on the reliability and expertise of your IT support services. However, managing an in-house IT team can be a daunting task, diverting precious time, resources, and attention away from your core business functions. It is precisely in this realm that outsourcing IT support services shines like a guiding beacon, offering a solution that empowers businesses with unparalleled advantages.
As the curtain falls on this exploration of the benefits of outsourcing IT support services, it becomes clear that entrusting your IT needs to external experts holds the key to unlocking productivity and unleashing your business’s full potential. By leveraging the skills and knowledge of a specialized IT support provider, you gain access to a team that is always at the forefront of technological advancements. Their relentless dedication and continuous training ensure that your systems are up-to-date, fortified with the latest security measures, and optimized to propel your business forward.
Engaging a reputable IT support service also grants you a competitive edge, particularly in today’s global landscape where businesses are relentlessly vying for success. Outsourcing allows you to tap into a vast pool of talent, drawing upon diverse expertise and experiences that transcend geographical boundaries. This global perspective injects your organization with fresh ideas, unique solutions, and a newfound agility that drives innovation and adaptability in the face of ever-evolving technological challenges.
Furthermore, the financial aspect cannot be ignored when contemplating outsourcing IT support services. The cost savings are undeniably substantial, with the elimination of expenses associated with maintaining an in-house IT team, including salaries, benefits, recruitment, and training costs. By aligning your IT support services with your business needs, outsourcing enables you to operate within a flexible budget, demystifying financial constraints while enhancing operational efficiency.
While it is true that relinquishing control of your IT functions may raise concerns, the resounding benefits of outsourcing far outweigh any initial apprehensions. With a trustworthy IT support partner, you can rest assured that your systems are in capable hands, bolstered by round-the-clock monitoring, rapid response times, and proactive problem-solving. This essential partnership allows you to refocus your attention where it matters most – nurturing your core business, fostering expansion, and catering to the needs of your valued customers.
As we conclude this illuminating examination of the benefits of outsourcing IT support services, it is evident that this strategic decision can transform your business’s IT operations, revolutionize efficiency, and drive substantial growth. Embracing the power of outsourcing signifies embracing a future where technology empowers your business, liberating your energy and resources to soar to new heights. With the right IT support services provider by your side, the world becomes a canvas on which your business’s success story is painted, stroke by stroke, with every keystroke.